How to spot a phishing email
Phishing scams are more common than you think. Some of these email scams are easily identifiable, while others hide behind an array of claimed legitimacies that are easily accepted by the unaware eye.
Whether you manage your own emails, or rely on someone else to do it for you, you could be vulnerable to human hacking.
Social engineering, sometimes referred to as “the art of human hacking”, involves the exploitation of weaknesses found in human psychology. In very basic terms, social engineers trick people into divulging information they would normally keep private, and is something that an awareness of cybersecurity principles can help to protect you against.
Let’s take a look at a popular example of social engineering in action:
phishing
ˈfɪʃɪŋ/
noun
the fraudulent practice of sending emails purporting to be from reputable companies in order to induce individuals to reveal personal information, such as passwords and credit card numbers, online.
So, now that you can answer the question “What is phishing?”, here are 5 ways to recognise a phishing scam, followed by a dissection of a real-life scenario: a PayPal phishing email.
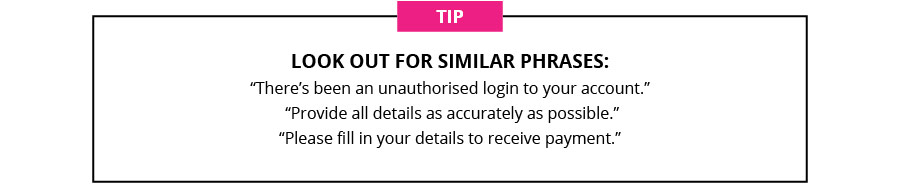
1. Request for personal information
Hear that? It’s the sound of alarm bells.
While a phishing email may attempt to gather other personal information, the common aim is banking details – for obvious reasons.
It’s highly unlikely that any bank, or other company, will ask for your personal information via email, so keep it to yourself.
And tell your secretary to do the same.
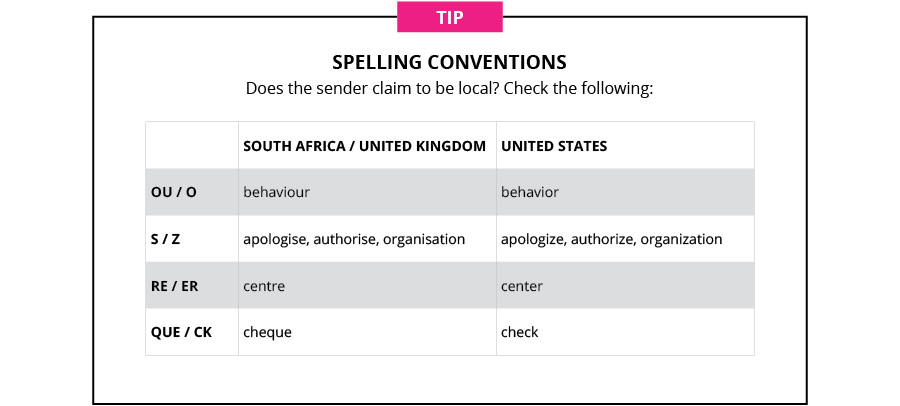
2. Spelling and grammar
Ever heard the saying “It takes a lifetime to build a good reputation, but you can lose it in a minute.”?
It’s a truth that every brand is, or should be, painfully aware of.
Brands are especially careful of avoiding simple mistakes – they look unprofessional and that’s mostly because if they happen, they are.
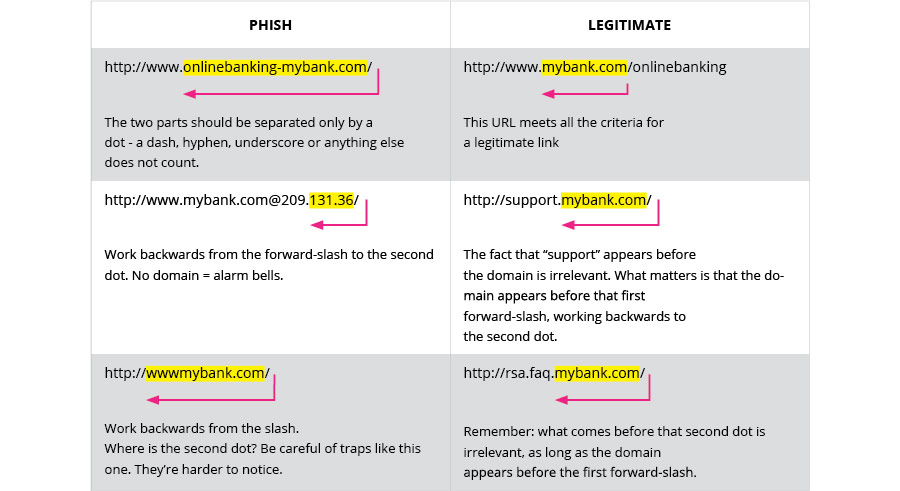
3. Suspicious links
Hyperlinked text can act as a false link. Instead of immediately clicking on a link in the body of your email, hover over it to see the actual address.
Is it what you expected? Or does it look something like this:
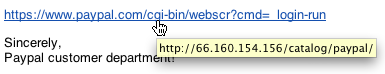
The main web address, or “domain”, consists of two parts separated by one dot (i.e. name(dot)com = paypal.com) and appears before the first forward-slash (after “http://”). If the domain doesn’t appear there, it’s likely a phish.
Work backwards from the forward-slash and stop at the second dot to determine the link’s legitimacy – what comes before that is irrelevant.
For example:
4. Urgency tactics
Let’s imagine your banking details really have fallen into the wrong hands. What’s a more likely course of action for your bank to take?
- Send you an urgent email or text message
- Call you immediately
It’s obvious, right?
However, “Why didn’t they call me?” might not be the first question that pops into your head when you’re reading an email telling you that someone has stolen your credit card details . You’re more likely to think, “ShitfuckballsohGod, how do I fix this?”
And that’s exactly what Phishermen take advantage of.
Watch out for:
Timing
“Take immediate action”
“You don’t have much time”
Punctuation
…
!!!
??
Scare tactics
“(Do this) to prevent the loss of all your savings.”
“Criminals could be spending your money right now.”
Full disclosure
Phishing scams usually go for an all-or-nothing approach, asking for everything from contact info and home address, to credit card details and names of family members.
5. The return addresses
Most return addresses are represented by a name rather than a full address – in the same way that a full link can be represented by a hyperlinked word or phrase.
Always check the full address. Here’s what it should look like:
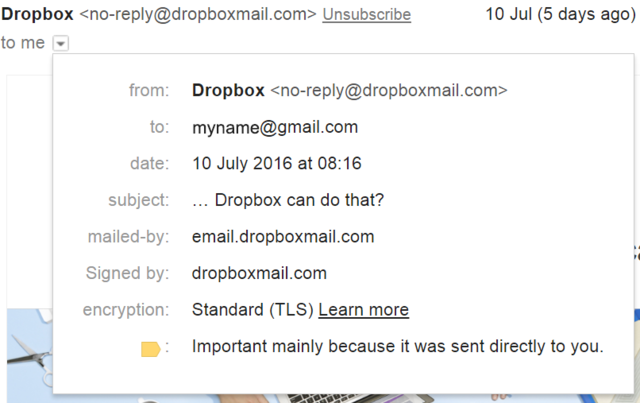
And here’s an example of what it might look like if it was a phish:
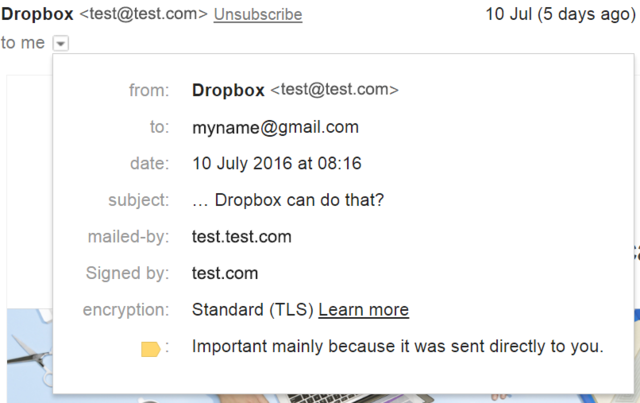
Just because it has the company name in the “from:” field doesn’t necessarily mean it’s legitimate.
TIP: The Greeting
Does the “Dear…” line greet you by name?
Most companies, especially your bank, have your personal information available and will address you by name in all communication.
Dissecting a real phishing email
How many warning signs can you see (from the surface), and what would you double-check that you can’t see in this mail? Once you’ve had a look, check the answers below.
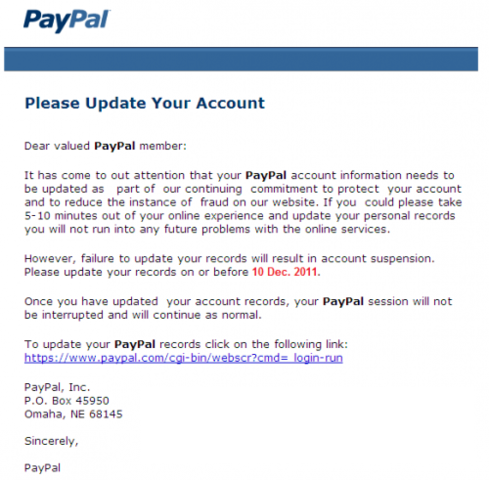
On the surface:
- The PayPal logo usually has “™” after it
- Not addressed to recipient’s name
- “PayPal” is in bold throughout the mail – why?
- Double spacing issues
- Urgency: “…before 10 Dec 2011”
- P.O. Box address is wrong
- Awkward sentences in some instances : “…take 5-10 minutes out of your online experience…”, “…your PayPal session will not be interrupted…”
Below the surface:
- Is the “from:” address legitimate?
- Is the link in the body of the email real, or a hyperlink to another address?
Want to protect your company from cyber fraud?
Fill the gaps in a lucrative industry experiencing a shortage of skilled professionals with UCT Fundamentals of Cyber Security online short course.